The Reality Behind the “Decentralized” Label in Crypto

One of my persistent frustrations with crypto content online is the lack of a clear, honest definition of decentralization. Most articles repeat it as a marketing slogan, but few actually examine how it works—or fails to work—in practice. After observing the industry for years, I decided to address this directly: no crypto wallet is truly decentralized.
For years, decentralization has been the primary sales pitch of the cryptocurrency industry. It is presented as a symbol of independence, privacy, and financial freedom. However, the reality is that even the most popular wallets, from MetaMask and Trust Wallet to various hardware options, are not as decentralized as their advertisements suggest.
While it is true that you control your private keys in these “self-custody” wallets, the infrastructure supporting these applications is often dependent on centralized servers, private companies, and code controlled by a small group of developers. Furthermore, many users are unaware of the volume of data these apps collect—ranging from IP addresses and technical device info to approximate locations.
The issue is not just about the term “decentralized.” It is about security, how data is transmitted, and the specific permissions these apps demand from your device. In this article, I will explain why even self-custody wallets operate with centralized dependencies. We will look at how MetaMask handles user data, the implications of Binance owning Trust Wallet, and the hidden risks within software libraries.
Theory vs. Practice
In the blockchain industry, decentralization theoretically means removing intermediaries. Ideally, no single entity should control transactions or access to data. Networks like Bitcoin and Ethereum were built on this logic: every node has an equal role, and decisions are made through consensus rather than a central command.
However, this decentralization often exists only at the network level, not at the tool level. A crypto wallet acts as an intermediary between you and the blockchain. It is a bridge designed to let you manage assets without needing deep technical knowledge. But these software bridges are exactly where “centralization” re-enters the picture. The paths used to communicate with the network—such as RPC services or data servers—are usually owned and managed by the company that created the wallet.
Simply put: you might own the keys to your house, but the company providing the front door controls the only path to the street. If they decide to close that path or monitor who walks through it, your “independence” is compromised.
The Illusion of Privacy in Popular Wallets
One of the biggest misconceptions in the crypto community is equating “private key ownership” with “decentralization.” Having your seed phrase means you are the legal owner of the assets, and no one can move them without that key. However, this does not mean your connection to the blockchain is decentralized.
When you use a wallet like MetaMask, your transaction data, wallet address, and IP address can be collected and sent to central servers. You hold the keys, but the developer controls the communication route. From the outside, the structure looks decentralized, but it relies on monitored, centralized infrastructure.
MetaMask: User-Facing Decentralization, Technical Centralization
MetaMask, developed by ConsenSys, serves millions of users. In 2022, the company confirmed that when users make transactions, it collects data—including IPs and wallet addresses—through a service called Infura.
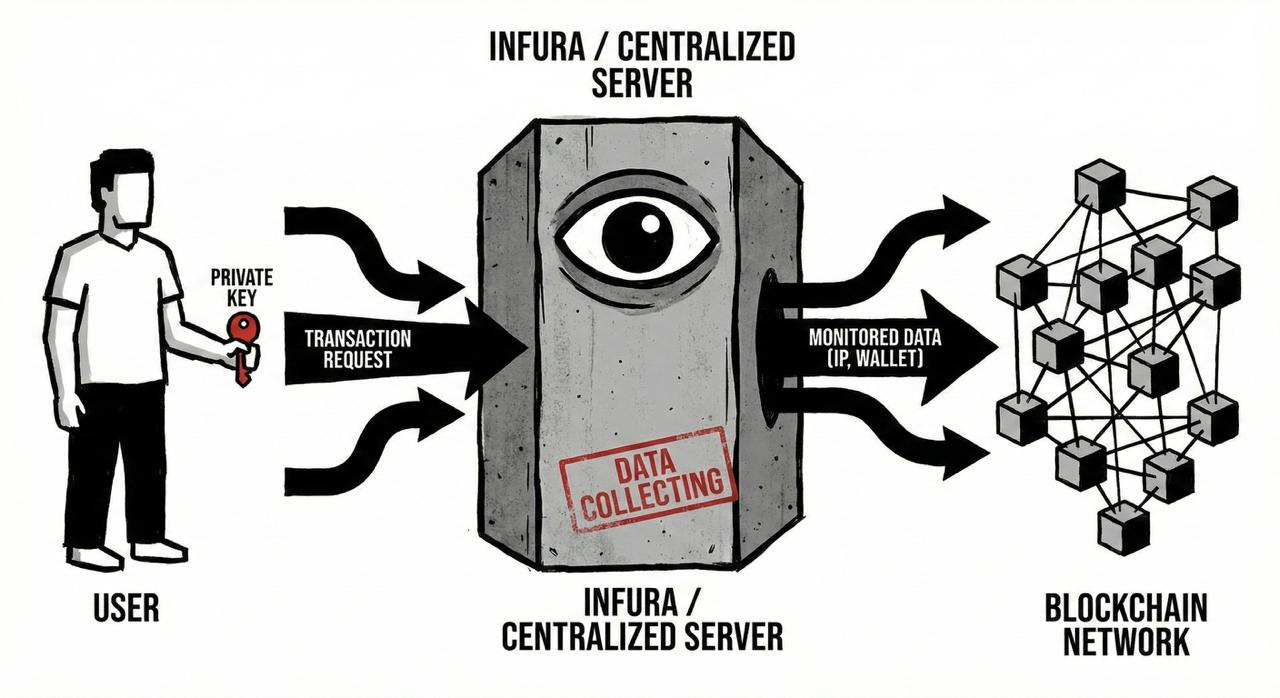
Infura is the default RPC (Remote Procedure Call) service MetaMask uses to talk to the Ethereum network. When you send a transaction, your data hits Infura’s servers first, rather than going directly to the blockchain. This means your privacy is managed by a single company. While public backlash eventually forced ConsenSys to reduce data retention to seven days and add an “opt-out” option, the core issue remains: the default experience is tethered to a centralized point of failure.
Furthermore, software updates are distributed from central servers. A developer can change security settings or access permissions in any new version, which contradicts the idea of “total user control.”
Trust Wallet: Independence Under the Shadow of Binance
On the surface, Trust Wallet is an independent, non-custodial wallet. But its background is different. While it isn’t directly under the SEC’s thumb, its ownership by Binance introduces specific risks.
Since 2023, Binance has faced significant regulatory challenges globally. For a Trust Wallet user, this ownership could lead to practical issues, such as disruptions in updates or geographical restrictions. Some blockchain security analysts argue that the main risk for Trust Wallet isn’t the code itself, but the centralized entity that owns and maintains it. If the parent company is forced to comply with specific regulations, the “independent” wallet may have to follow suit.
Physical Security vs. Hidden Software Risks
Hardware wallets like Trezor, Ledger, and SafePal are often marketed as the ultimate security solution because they store private keys offline. While they are indeed safer than “hot wallets,” they are not immune to centralized failures.
In 2020, Ledger experienced a massive data breach. The personal information of over 270,000 users—names, emails, phone numbers, and home addresses—was leaked from their marketing database. Even though the private keys remained safe, users became targets for phishing attacks and physical threats. This incident proved that even if your key is offline, your identity remains in the hands of a centralized company.
Hidden Permissions and App Behavior
Beyond corporate ownership, the wallet applications themselves can gather significant data. When you grant a wallet permission to use your camera for scanning QR codes, the app technically gains access to that hardware. I recommend giving only “one-time” permissions rather than permanent access to mitigate this risk.
Most wallets also collect “Analytics” without clearly informing the user. They track how many hours you use the app, your transaction types, and which exchanges you interact with. While companies claim this is for “User Experience,” it creates a detailed profile of your financial habits and behavioral patterns.
Vulnerabilities in Software Libraries
No wallet is built entirely from scratch. Developers use “Third-Party Libraries”—pre-written code—to handle complex tasks like encryption or network communication. Using these libraries speeds up development but introduces a single point of failure. If one library contains a bug or a malicious backdoor, millions of users are instantly exposed.
A real-world example occurred between 2018 and 2019 regarding a flaw in a private key generation library. This library was used in various projects, including some referenced by Andreas Antonopoulos. A bug in the “Random Number Generation” caused some devices to produce weak, predictable private keys.
In crypto, a predictable key is a disaster. It allows hackers to calculate your key and drain your funds. This event demonstrated that even with good intentions and open-source transparency, a tiny error in a randomizing function can destroy the security of the entire system. Hackers don’t always need to break in from the outside; sometimes the door is left unlocked by the code itself.
Centralized Failures and the Spectrum of Security
The June 2023 hack of Atomic Wallet serves as a stark reminder of these internal risks. In this attack, North Korea’s Lazarus Group reportedly stole over $100 million from users. While early estimates by security firms put the loss lower, the FBI later confirmed the full scale of the damage.
The vulnerability was not an external breach of the blockchain itself; it was a flaw within the wallet’s own software. A weakness in the desktop application’s code allowed attackers to access user private keys. This incident highlights that even a wallet calling itself “self-custody” can undermine the entire philosophy of decentralization with a single line of bad code.
Interestingly, the development team later offered compensation to some victims. While this was a positive gesture, it ironically proves the existence of a centralized decision-making system. If a system were truly decentralized, there would be no central entity capable of managing a crisis or deciding on compensation.
The 2025 Data Leak: 16 Billion Records
Further proof of infrastructure vulnerability came in June 2025, during one of the largest data leaks in history. Over 16 billion accounts from 30 insecure databases were exposed, including login credentials for Google, Apple, and various crypto platforms. Sensitive data like session tokens and files containing seed phrases were leaked.
The source was a combination of malware—RedLine and Raccoon Stealer—exploiting insecure cloud storage like Amazon services. While no specific wallet was “hacked” directly, many MetaMask and Trust Wallet users lost funds because they stored their keys on infected devices. This shows that decentralization only matters if every link in the chain—from your OS to your storage—is equally secure.
A Relative Spectrum
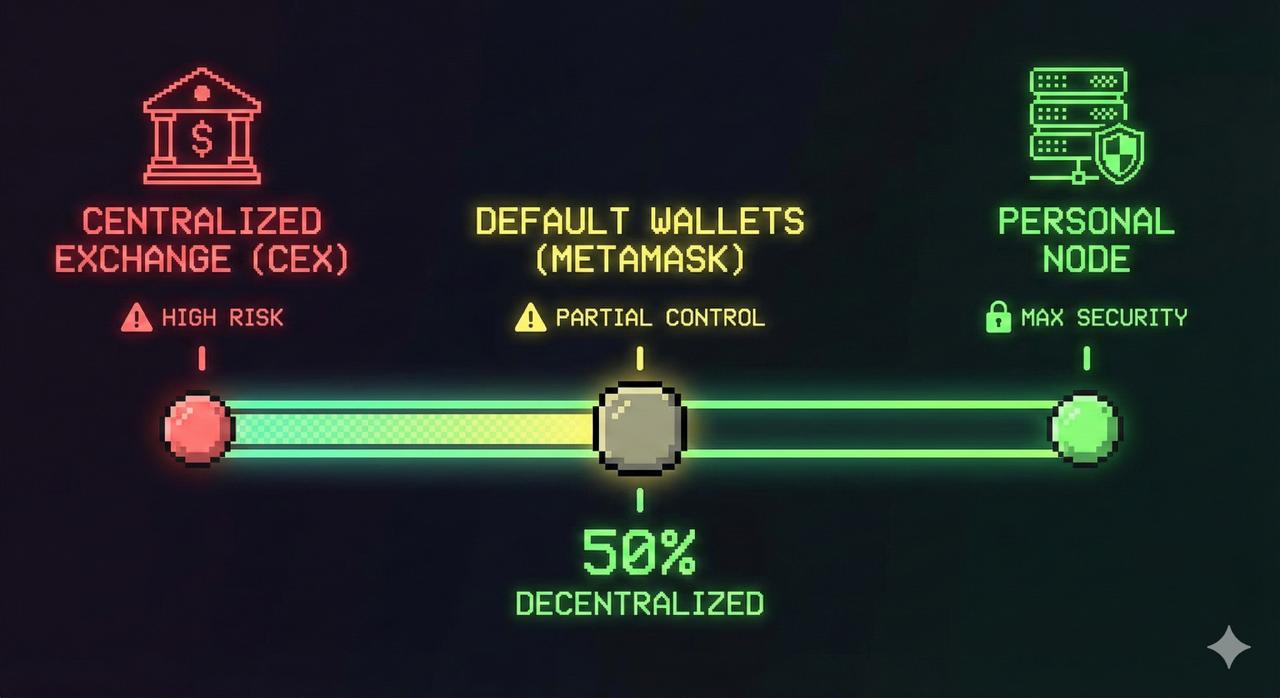
I believe we should stop viewing decentralization as a binary “yes or no” status. It is a spectrum.
-
What you truly control: In most self-custody wallets, your private key and seed phrase are stored on your device. If you lose them, the company cannot recover your funds. This is the only part that is truly yours.
-
What remains centralized: Most users rely on default settings, meaning their connection to the blockchain goes through the developer’s servers. Software updates, error reports, and analytics are all managed centrally, often on servers hosted in jurisdictions like the US or Europe, subject to local laws.
Advanced users can mitigate this by running their own Personal Node or using a private RPC. However, for the average person, this requires technical knowledge and hardware costs that are simply not practical.
And..
The claim of “decentralization” in the wallet industry is often more of a marketing exaggeration than a technical reality. Real security in crypto does not come from high-energy slogans or using multiple apps; it comes from understanding how these tools actually function.
True independence requires awareness. You must manage your app permissions, disable tracking analytics, and understand that you are always operating within a web of centralized dependencies. Decentralization is an ideal we strive for, but in the real world, your security depends on your own knowledge of where the “centralized” risks are hidden.